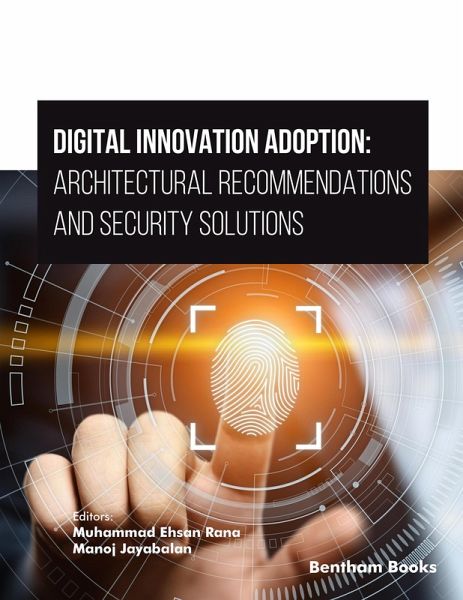
Digital Innovation Adoption: Architectural Recommendations and Security Solutions (eBook, ePUB)

PAYBACK Punkte
0 °P sammeln!
This reference reviews the architectural requirements of IT systems that are designed to digitally transform business operations. It is a compilation of 7 timely reviews that demonstrate how adopting emerging technologies and examining the security-based concerns can lead to innovation in the business sector. The aim of the book is to guide scholars and business consultants on IT and business frameworks that can help new and existing organizations navigate the challenges posed by disruptive technologies to create a competitive advantage. The reviews are contributed by experts in business and i...
This reference reviews the architectural requirements of IT systems that are designed to digitally transform business operations. It is a compilation of 7 timely reviews that demonstrate how adopting emerging technologies and examining the security-based concerns can lead to innovation in the business sector. The aim of the book is to guide scholars and business consultants on IT and business frameworks that can help new and existing organizations navigate the challenges posed by disruptive technologies to create a competitive advantage. The reviews are contributed by experts in business and information technology. The chapters cover diverse topics related to technological advancements and digital security measures. Chapter 1 offers insights into accessing and securing patient medical records through a blockchain-based framework, detailing research methodology, scalability, and standards. Chapter 2 discusses cyber threats in IoT-connected cars, addressing vulnerabilities, attack methods, and defense strategies. Chapter 3 focuses on malware analysis and detection using machine learning techniques. Chapter 4 emphasizes on securing IoT-based home automation. Chapter 5 presents an IoT policy and governance reference architecture to ensure integrity and security across devices. Chapter 6 explores organizational security improvements to prevent deepfake ransomware. Finally, Chapter 7 examines the use of machine learning in credit card fraud detection, discussing challenges and control layers. Readership Scholars, academics, business consultants, entrepreneurs.
Dieser Download kann aus rechtlichen Gründen nur mit Rechnungsadresse in A, B, BG, CY, CZ, D, DK, EW, E, FIN, F, GR, H, IRL, I, LT, L, LR, M, NL, PL, P, R, S, SLO, SK ausgeliefert werden.