Managing an Estate Without Paper Records (eBook, ePUB)
Versandkostenfrei!
Sofort per Download lieferbar
6,49 €
inkl. MwSt.
Weitere Ausgaben:

PAYBACK Punkte
0 °P sammeln!
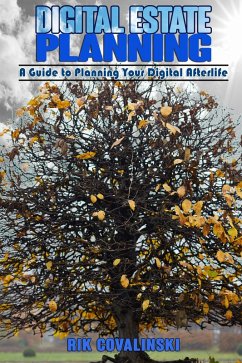
\Managing an estate after the death of a loved one is hard. It is especially hard if there are no paper records. This book, based on the author's experience, shows how to do this. Specific items discussed include:Setting up the estateBecoming the Administrator/Personal RepresentativeTax records and tax reportingGetting into the deceased person's computerGaining access to existing bank brokerage and treasury accountsFinding missing fundsCreating business records from scratchSocial SecurityNavigating the privacy policies of many tech companiesPlanningLeaving a digital legacyOnly minimal computer...
\
Managing an estate after the death of a loved one is hard. It is especially hard if there are no paper records. This book, based on the author's experience, shows how to do this. Specific items discussed include:
Setting up the estate
Becoming the Administrator/Personal Representative
Tax records and tax reporting
Getting into the deceased person's computer
Gaining access to existing bank brokerage and treasury accounts
Finding missing funds
Creating business records from scratch
Social Security
Navigating the privacy policies of many tech companies
Planning
Leaving a digital legacy
Only minimal computer literacy is needed to understand this book.
Managing an estate after the death of a loved one is hard. It is especially hard if there are no paper records. This book, based on the author's experience, shows how to do this. Specific items discussed include:
Setting up the estate
Becoming the Administrator/Personal Representative
Tax records and tax reporting
Getting into the deceased person's computer
Gaining access to existing bank brokerage and treasury accounts
Finding missing funds
Creating business records from scratch
Social Security
Navigating the privacy policies of many tech companies
Planning
Leaving a digital legacy
Only minimal computer literacy is needed to understand this book.
Dieser Download kann aus rechtlichen Gründen nur mit Rechnungsadresse in A, B, CY, CZ, D, DK, EW, E, FIN, F, GR, H, IRL, I, LT, L, LR, M, NL, PL, P, R, S, SLO, SK ausgeliefert werden.