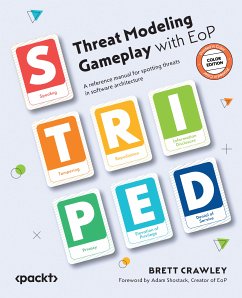
Each chapter in this book covers a suit in the Elevation of Privilege (EoP) card deck (a threat category), providing example threats, references, and suggested mitigations for each card. You'll explore the methodology for threat modeling-Spoofing, Tampering, Repudiation, Information Disclosure, and Elevation of Privilege (S.T.R.I.D.E.) with Privacy deck and the T.R.I.M. extension pack. T.R.I.M. is a framework for privacy that stands for Transfer, Retention/Removal, Inference, and Minimization. Throughout the book, you'll learn the meanings of these terms and how they should be applied. From spotting vulnerabilities to implementing practical solutions, the chapters provide actionable strategies for fortifying the security of software systems.
By the end of this book, you will be able to recognize threats, understand privacy regulations, access references for further exploration, and get familiarized with techniques to protect against these threats and minimize risks.
Dieser Download kann aus rechtlichen Gründen nur mit Rechnungsadresse in A, B, BG, CY, CZ, D, DK, EW, E, FIN, F, GR, H, IRL, I, LT, L, LR, M, NL, PL, P, R, S, SLO, SK ausgeliefert werden.